Dev Machine Guard
by step-security
Scan your dev machine for AI agents, MCP servers, IDE extensions, and suspicious packages - in seconds.
No known CVEs
Apache-2.0 license
Actively maintained
Last commit 5d ago
Works with most clients
Transport: stdio, sse
0 tools
Grade F
Step 1
Install in your client
Config is the same across clients — only the file and path differ.
CD
Supported in Claude Desktopstdio, sse · Node 18+
Paste into ~/Library/Application Support/Claude/claude_desktop_config.json
{
"mcpServers": {
"dev-machine-guard": {
"args": [
"mcp-remote",
"https://api.stepsecurity.io"
],
"command": "npx"
}
}
}Are you the author?
Add this badge to your README to show your security score and help users find safe servers.
Embed in your READMEAbout badges →
[](https://mcppedia.org/s/dev-machine-guard)
Read me
What Dev Machine Guard does
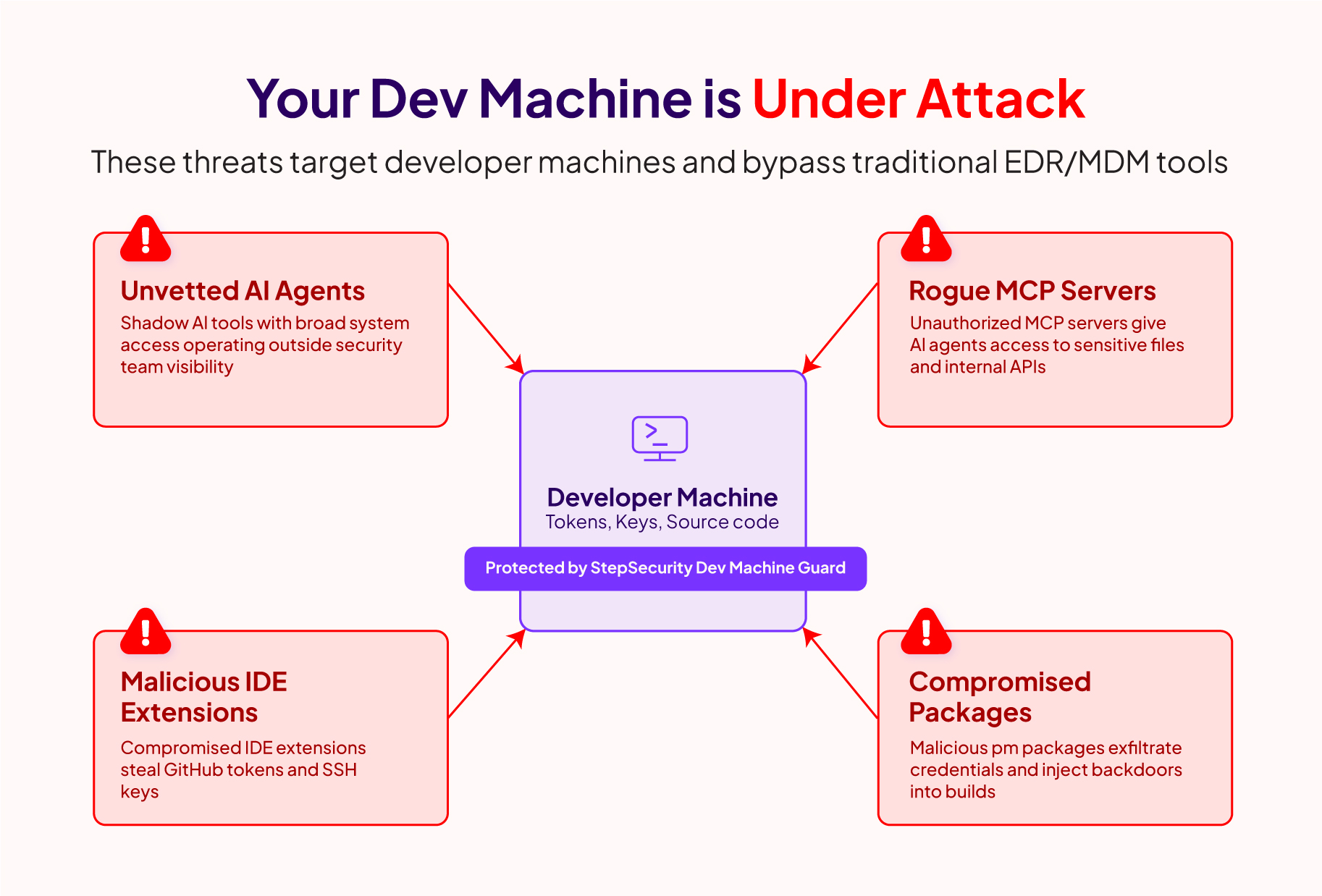
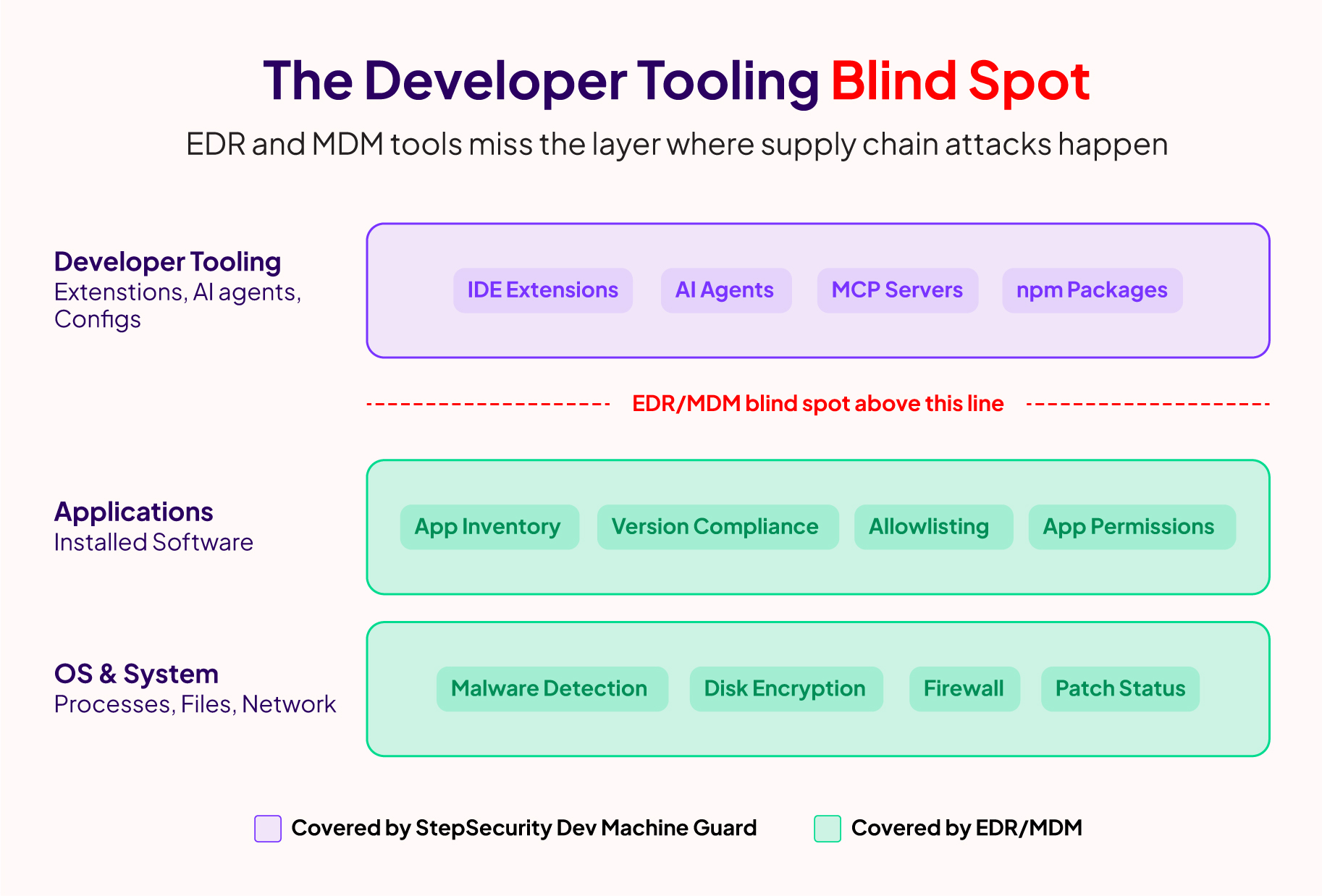
Developer machines are the new attack surface. They hold high-value assets — GitHub tokens, cloud credentials, SSH keys — and routinely execute untrusted code through dependencies and AI-powered tools. Recent supply chain attacks have shown that malicious VS Code extensions can steal credentials, rogue MCP servers can access your codebase, and compromised npm packages can exfiltrate secrets.
Test This Server
No automated test available for this server. Check the GitHub README for setup instructions.
Loading README…
Scored, not listed
Why this score
Five weighted categories — click any category to see the underlying evidence.
Score breakdown
45/100across 5 weighted dimensions
0255075100
15
14
10
−55
Security
Maintenance
Efficiency
Documentation
Compatibility
Categoriesclick a row to see evidence
Security
OSV.devNo known CVEs.
No package registry to scan.
Community
Reviews
Be the first to review
Have you used this server?
Share your experience — it helps other developers decide.
How easy was setup?Did it work reliably?How was the documentation?
Sign in to write a review.
Frequently Asked Questions
- Is Dev Machine Guard safe to use?
- Dev Machine Guard has no known CVEs as of the latest MCPpedia security scan. It does not require authentication, so any local process can connect — keep this in mind in shared environments. Licensed under Apache-2.0.
- How do I install Dev Machine Guard?
- Dev Machine Guard supports copy-paste install configs on its MCPpedia page for Claude Desktop, Cursor, and Claude Code. Scroll to the Quick Install section and select your client.
- What AI clients work with Dev Machine Guard?
- Dev Machine Guard is compatible with claude-desktop, cursor, claude-code. It uses stdio and sse transport.
- Is Dev Machine Guard actively maintained?
- Dev Machine Guard is actively maintained — last commit was 5 days ago. It has 140 GitHub stars.
Related
Similar servers
Others in security
An evil MCP server used for redteam testing
30 1
AI-powered reverse engineering assistant that bridges IDA Pro with language models through MCP.
9.0k 3
I
io.github.jasonxkensei/xproof92Proof primitive for AI agents on MultiversX. Anchor file hashes on-chain as verifiable proofs.
1 1
mcpki-server is the backend infrastructure for https://www.mcpki.org, enabling secure public key management and autonomous certificate handling for large language models (LLMs).
10
MCP Security Weekly
Get CVE alerts and security updates for Dev Machine Guard and similar servers.
Community
Discussion
Start a conversation
Ask a question, share a tip, or report an issue.
Has anyone used this with Cursor?How do you handle auth?Any alternatives?
Sign in to join the discussion.