Identity Service
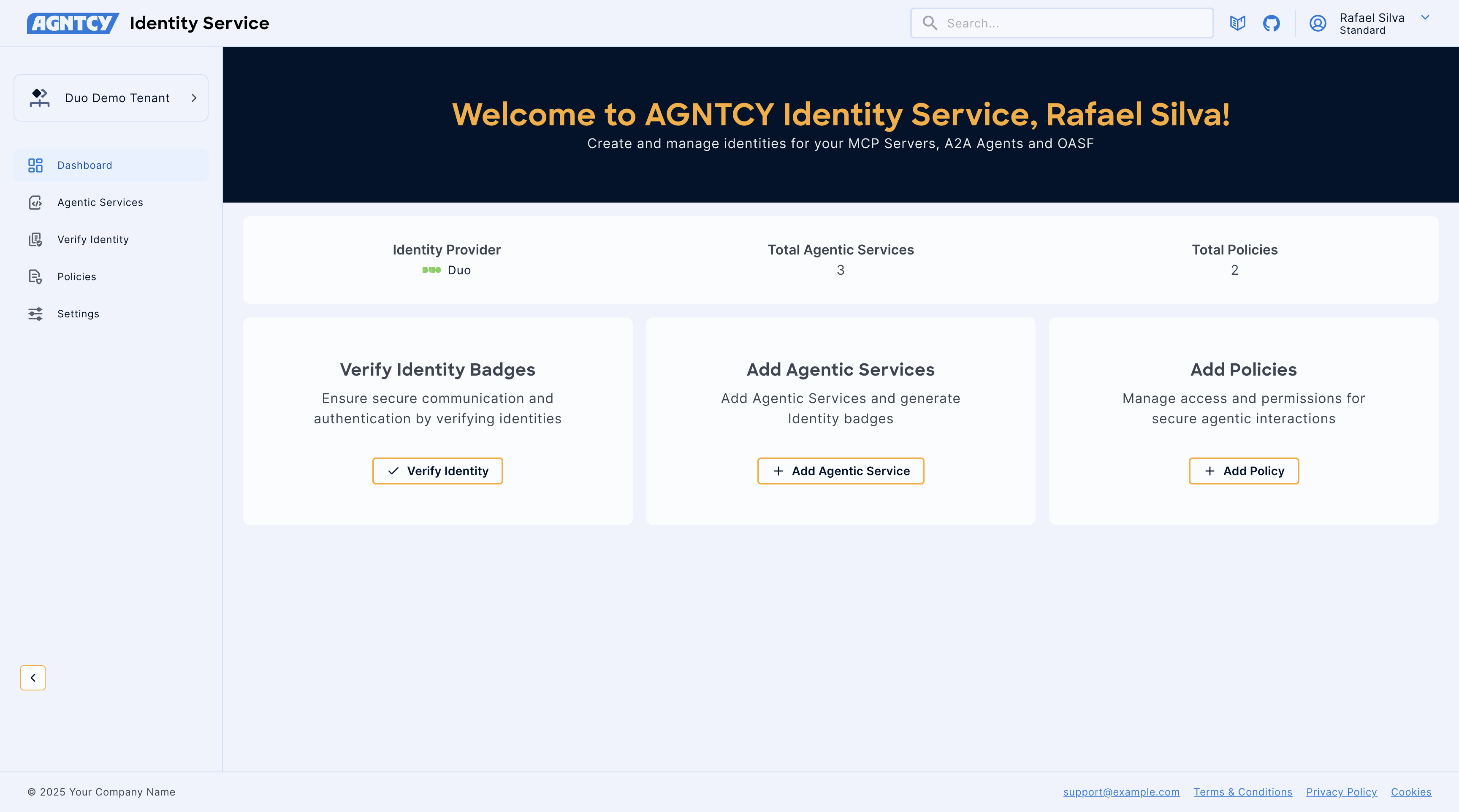
AGNTCY Identity Service serves as the central hub for managing and verifying digital identities for your Agentic Services.
ActiveNot tested
★ 61GitHub
32DNo CVEsactiveApache-2.0
Quick Install
{
"mcpServers": {
"identity-service": {
"command": "<see-readme>",
"args": []
}
}
}No install config available. Check the server's README for setup instructions.
Are you the author?
Add this badge to your README to show your security score and help users find safe servers.
Embed in your READMEAbout badges →
[](https://mcppedia.org/s/identity-service)
Should you use this server?
AGNTCY Identity Service serves as the central hub for managing and verifying digital identities for your Agentic Services. In today's interconnected digital landscape, secure and reliable identity management is paramount. AGNTCY Identity Service addresses this need by providing a streamlined service to:
✓
Is it safe?
No package registry to scan.
No authentication — any process on your machine can connect.
Apache-2.0. View license →
✓
Is it maintained?
Last commit 16 days ago. 61 stars.
i
Will it work with my client?
Transport: sse. Compatibility not confirmed.
Test This Server
No automated test available for this server. Check the GitHub README for setup instructions.
Score Breakdown
Security
6/30No known vulnerabilities.
○
Known CVEs — No package registry to scan
○
Tool safety — No tools to analyze
○
Tool poisoning — No tools to analyze
○
Injection vectors — No tools to analyze
✓
Tool stability — Tool definitions stable
○
Dependency health — No package to analyze
✓
License — License: Apache-2.0
○
Authentication — No authentication required
○